All about Hacking,tools,Network Security Tools,Ethical Hacking, Penetration Testing & Computer Security
Saturday, May 9, 2009
Great Collection Of Hacking Books (All Hacking Books from A-Z)
Great Collection Of Hacking Books (All Hacking Books from A-Z) is available on a new fast direct download service with over 2,210,000 Files to choose from.Download anything with more then 1000+ Kb/s downloading speed.Signup process takes just 10 sec to go.Signup today and enjoy the speed !
http://uploading.com/files/PAQSUV0D/Collection_of_Hacking_Ebooks_Part1.rar
http://uploading.com/files/JPVAHTMA/Collection_of_Hacking_Ebooks_Part2.rar
http://uploading.com/files/JPVAHTMA/Collection_of_Hacking_Ebooks_Part3.rar
Friday, May 8, 2009
Hacking Book Collection (EBooks,Tutorial)
- BlueTooth Hacking
- Ethical Hacking
- Google Hacks
- Hack & Crack
- Hack Attacks Revealed
- Hack Attacks Testing - How To Conduct Your Own Security Audit
- Hack IT Security Through Penetration Testing
- Hack Proofing Your Network - Internet Tradecraft
- Hack Proofing Your Network Second Edition
- Hack Proofing Your Web Server
- Hack The Net
- Hack Xbox 360
- Hackers Black Book
- Hacking Firewalls And Networks How To Hack Into Remote Computers
- Hacking a Coke Machine
- Hacking and Network Defense
- Hacking for Dummies
- Hacking Intranet Websites
- Hacking Techniques
- Hacking The Cable Modem
- Hacking The Linux
- Hacking Web Applications
- Hacking Windows XP
- Hacking PSP
- Kevin Mitnick - The Art of Deception
- Kevin Mitnick - The Art of Intrusion
- Network Security Hacks - Tips & Tools For Protecting Your Privacy
- PayPal Hacks
- PC Hacks
- Simple Hacks - Addons, Macros And More
- The Database Hacker Handbook Defending Database Servers
- Wireless Hacking
- Wireless Network Hacks & Mods for Dummies
http://rapidshare.com/files/56561574/Hacking_e-Book.part1.rar
http://rapidshare.com/files/56567737/Hacking_e-Book.part2.rar
Tuesday, May 5, 2009
Google launches stand-alone contacts manager
Aimed at letting users share contacts more easily between different services, Google Contacts works like any other contacts function. You can import and export your contacts from other sources such as Outlook, Outlook Express, Yahoo, or Hotmail. For Apple you must use a utility called "A to G."
If you are part of a business, school or other organization using Google Apps, the administrator will have to enable this functionality within the control panel by clicking on the "add more services" link, finding the "Contacts" option and clicking the "add it now" button.
Monday, May 4, 2009
Know the Ethics and Learn Computer Hacking
Internet has become a bandwagon of entertainment, education and business. It beats tradition mediums in terms of the benefits it offers. But unfortunately there is much scope of anonymity/privacy on the web and helps the cyber terrorists prey up on the internet resources. That’s why, it is encouraged to learn computer hacking to counter the actions of unethical hackers (also known as black hats).
Hacking is a fraudulent act that is illegal in some ways and helpful in others. It is to know the programmable systems and how they work in a network. An ethical hacker shows the downfalls in the security system of an organization so they can improve it. Today hacking has become an art and very popular that hackers have formed groups and even have conferences together to share their knowledge. Hacking for whatever the purpose, good or bad, requires knowledge and much programming skills. An intelligent programmer can be a good ethical/unethical hacker. These days "hacker" is being used as a term for expert, intelligent and creative people. Let’s discuss how to learn computer hacking:
10 Tips to Learn Computer Hacking
As told before, professional hackers are generally more intelligent than any average programmer. So becoming a hacker depends a lot on one’s intelligence and efforts. However, the following tips will help you learn computer hacking in a systematically.
- Be curious: Curiosity is the mother of hacking. Look under the hood. Take things apart. Know the details of your system directories, file systems, system files. Look inside your computer.
- Read a lot: Buy lots of books, go through the tutorials. Read the help files on your system. If you are using Linux/Unix read the man files.
- Experiment: Take precautions and experiment whatever you read. Apply to work the idea that just hit your mind. Don't be afraid to change things. Doing this for a long time will give you much idea on the computer hardware and the operating system. Try using command options and switches. Tweak the registry and see what happens. Change settings in .INI files. In Linux/Unix, visit the directories where you normally don’t need to go.
- Make backups: If you start mucking around with system files, registries, password files, and such, you will eventually destroy your system. Have a backup ready. If you can afford it, have a system you use just for experimenting, ready to reload on a moment's notice, and do your serious work (or serious gaming!) on a different computer.
- Think out of box: Hacking is not restricted to computers only. You can try trick on other networks also like mobile, telephone, etc.
- Get some real tools: You can find numerous hacking tools on the net. Though some serious tools are not available for free, you need to have some Hex file editors, Snoopers, Compilers and APIs. In addition you also need Scripting tools, Disk editors/formatters and Disassemblers.
- Learn to program: Serious ethical hackers are always very good programmers. If you want to be a hacker, you're going to learn much programming. You should also be quite familiar with the popular operating systems like Windows, Linux, Unix, OS2 etc. Of course, the choice of language depends on you. In Unix and Unix-like OS (Linux, Free BSD) Perl is very good to start with. Use VB or Java to program in Windows. Which ever platform you use, you need to learn considerable C/C++. You should know more than one language because no one language is right for every task.
- Discuss with peers: In isolation, you can’t learn anything. You need to take classes, join users groups and computer clubs. Talking to people on IRC or other chat programs proves really helpful. Share what you learn. Because to get something you have to give some.
- Do some projects: Pick some projects and work consistently until you've finished them. Real time experience is better than reading. Build from ground zero, learn to create icons, associate it with some files, read how the search engines search, try to manipulate the programs that you use daily.
- Use the Internet: There is no source greater than the Internet. Start with the Web. Learn how to use Boolean searches. Bookmark all those sites which you find worth visiting. Sometimes you will find useful information at the most strangest places.
Detailed Courses of Study to Learn Hacking
- Techniques: Windows Hacking, Registries Editing, Password cracks, Google hacking, Computer Forensics, Firewalls, Network Hacking, Security tools, Hacking tools, Encryption, Email tracking, Router Hacking, Email Forging, Port Scanning , MAC Address Spoofing, Proxies etc.
- Tools: Key loggers, Anti Key Loggers, Firewalls, MAC Address Spoofing, Proxy Bouncing tools, Network Scanners like IPscan, Sniffers, Spyware and Trojan Detectors, Information Gathering Tools, Remote Administration Tools, Computer Forensics Tools, Steganography tools and a lot more.
- Games: Hacking Simulation Games to understand the world of hacking and provides you with the opportunity to practice hacking without the danger of getting caught
10 Commandments of Ethical Hacking
- Don’t a computer to harm other people.
- Don’t interfere with other people's computer work.
- Don’t snoop around in other people's computer files.
- Don’t use a computer to steal.
- Don’t use a computer to bear false witness.
- Don’t copy or use proprietary software for which you have not paid.
- Don’t use other people's computer resources without authorization or compensation.
- Don’t appropriate other people's intellectual output.
- Think about the social consequences of the program you are writing.
- Always use a computer in ways that insure consideration and respect for your fellow humans.
Saturday, May 2, 2009
Cain & Abel 4.9.18-password recovery
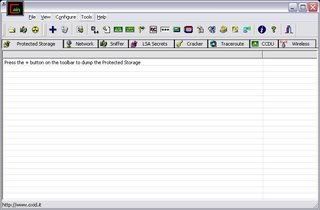
Cain & Abel 4.9.18-password recovery | 6,9 Mb
Cain & Abel has been developed in the hope that it will be useful for network administrators, teachers, security consultants/professionals, forensic staff, security software vendors, professional penetration tester and everyone else that plans to use it for ethical reasons. The author will not help or support any illegal activity done with this program. Be warned that there is the possibility that you will cause damages and/or loss of data using this software and that in no events shall the author be liable for such damages or loss of data. Please carefully read the License Agreement included in the program before using it.
The latest version is faster and contains a lot of new features like APR (Arp Poison Routing) which enables sniffing on switched LANs and Man-in-the-Middle attacks. The sniffer in this version can also analyze encrypted protocols such as SSH-1 and HTTPS, and contains filters to capture credentials from a wide range of authentication mechanisms. The new version also ships routing protocols authentication monitors and routes extractors, dictionary and brute-force crackers for all common hashing algorithms and for several specific authentications, password/hash calculators, cryptanalysis attacks, password decoders and some not so common utilities related to network and system security.
ADrive:
FileFactory:
RapidShare:
Hacker's Tool Set (45 Hacking Tools)

Features:
• IMC Grahams Trojan
• IMC Ice Dragon
• Myspace Password Cracker
• IMC Myspace Phisher
• Ultra Surf
• Rapid Share *** Gen
• MSN Nudge Madness
• Ice Reloaded MSN Freezer
• IMC Handbook
• BrutusAE2
• Lord PS
• Hoax Toolbox
• IMC Word List
• Blues Port Scanner
• Bandook RAT v1.35
• Project Satan 2.0
• EES binder v1.0
• File Injector v3
• Remote Desktop Spy v4.0
• Passive Terror v1.3 Final Edition
• Dyn-DL (Dynamic downloader)
• Silent Assassin v2.0
• Net Scan Tools v4.2
• Rocket v1.0
• NStealth HTTP Security Scanner v5.8
• Attack Toolkit v4.1 & source code included
• Legion NetBios Scanner v2.1
• Battle Pong
• TeraBIT Virus Maker v2.8
• p0kes WormGen 2.0
• JPS Virus Maker
• IRC Ban Protection
• IRC Mega Flooder
• FTP Brute Hacker
• RAR Password Cracker
• Vbulletin 3.6.5 Sql Injection Exploit
• IPB 2-2.1.5 Sql Injection Exploit
• IPB 2-2.1.7 Exploit
• Cain & Abel v4.9.3
• NetStumbler 0.4.0
• Cryptor 1.2
• VNC Crack
• Hamachi 0.9.9.9
• pbnj-1.0
• Mutilate File Wiper 2.92
• and many more...
US, EU, RU and Canada Download from Uploading
Download Here
PHI and Rest of the World Download from Good
Download Here
All-In-One Ultra Hacker
found this AIO did download just posting
This AIO is with viruses cos these are hacking tools and AV detect as viruses!
I think it's better to use deep freeze and than u can freeze ur pc when u use this tools and than u can unfreeze it when u don't use !
Includes:
AddrView.rar
AnonFTP.zip
AOL new.rar
AppToService.rar
arpinject.zip
aspack21.zip
Astaroth Joiner v2.rar
atk-2.1.zip
BankOfAmerica.rar
bios_pass_remover.zip
BlasterW32.zip
blue.zip
bmpripper.zip
brutus.zip
Cable Modem Sniffer.rar
CapKeys_DIGITAL.rar
CASXM138.zip
CAYZODQF.zip
CGI Founder v1.043.zip
cgis4.zip
CGISscan.zip
cia10.zip
cports.rar
craagle.zip
Crackftp.zip
CreditCardGjenerator.rar
Davs_TR_REtail.zip
DDL Sites.rar
DeepUnFreez.zip
DrVBS.zip
eBay.rar
EESBinder.zip
egold.rar
E-mail Cracker.rar
ezDataBase_Defacer.rar
F.B.I - Binder.rar
FTP Brute Forcer.rar
ftpbr.zip
~Censored~ Mail Bomber 2.3.rar
G00B3RS_phpBB_exploit_pack.rar
genxe-beta-0.9.0.zip
Google_Hacker_1.2.rar
grinder1.1.zip
Hack FLASH Template.zip
Hack MY Space.zip
Hack Photoshop CS2.zip
HackersAssistant.zip
HackTheGame.zip
hck.zip
hlboom.zip.zip
Hook Tool Box.rar
Hotmail Email Hacker.rar
Hotmail HAcker Gold.rar
Hotmail ScamPage.zip
HotmailHack.rar
HSBC-US.rar
hydra-4.6-win.zip
iecv.rar
IP2.rar
ipnetinfo.rar
john-17w.zip
Key Changer.rar
Key_Logger.zip
Legion NetBios Scanner v2.1.zip
Mail Boomb_2.0 YAHOO.zip
MIDNITEmassacre.zip
MooreR Port Scanner.rar
MSN Flooder 2.0.rar
MSN Messenger Account Cracker v2.0.rar
MSNLoader.rar
NET BIOS Scaner.rar
NetBIOS Name Scanner.rar
NetResView.rar
NFO Maker 1.0.zip
Nimda.zip
nkedb.zip
nolimitcracker.rar
NTPacker.zip
nts.zip
NullAddFrontend.zip
On-Off MSN.rar
OS Update Hack.rar
P0kes WormGen 2.0.zip
panther.zip
PayPal.rar
PCAnyPass.rar
Php Nuke Hacker v11.0.rar
phpBB Annihilator.rar
phpbb attack.rar
phpbb bruteforcer.rar
PhpBB pass extractor.zip
phpBB_DoS.rar
phpbb_spammer.rar
phpBBAttacker.rar
phpBBAttacker.zip
phpBBcracker.rar
PhpBuGScan.rar
~censored~.rar
PhpNuke_bypass.rar
Ping & Nukes.rar
Port Listener XP.rar
pqwak2.zip
procexp.rar
ProMo.rar
ProxyPro.zip
Pure phpBB Email harvester.rar
rainbowcrack-1.2-src win-lin.zip
Remote Shut Down.rar
ResHacker.zip
Rocket.zip
rpc.zip
RpcScan101.zip
Sasser.zip
SendMailer.zip
Server 2003 Keygen.rar
Server Killer.rar
showpassv10.zip
sitedigger2.zip
smbat-win32bin-1.0.4.zip
SMBdie.zip
smbproxy-win32bin-1.0.0.zip
Source Checker.rar
source codes.rar
sprut.zip
SQLScan v1.0.rar
Stealth - HTTP Scanner v1.0 build 23.zip
super.zip
SuperScan4.rar
tftpd32.273.zip
thunter.zip
TinaSoft KILL.zip
traceroute.rar
UC.Forum Spam.rar
udpflood.zip
Ultra Dos.zip
USBank.rar
Visa Spam.zip
Warez Sites.rar
Web Cracker 2.0.rar
WebCracker 4.0.rar
whoistd.rar
Win XP Activator.rar
WindowHide.rar
Windows XP Corperate Keygen.rar
Windows XP KeyGen.rar
Windows XP Product Key Changer.rar
Windows XP Product Key Checker.rar
Windows XP Product Key Viewer.rar
WindowsAdminpasswordHack.rar
wwwhack.rar
xpass.zip
xplizer.rar
Yahoo Password.zip
yahooUltraCracker.rar
zehir.zip

All-In-One Ultra Hacker (2008)
Three Most used Backdoor Programs
There is a general misconception about security today. Most people would love to believe that their firewalls are completely capable to protect them from anything indecent. The sad part, they could not be more wrong. Hungry Hacker aim to prove it with three separate programs that can compromise the security of computers. You have the opportunity to say “What’s a backdoor?” Yes, these programs were created in 1990, but still pose a real threat today. It is the first two that are still being developed.
Using these programs any noob can remotely access your computer without any Authentication and do whatever he wants. I will tell you some of the features rest of them you need to try it and find out. These Programs :
- Work as a key logger.
- Send any Information from Victim’s PC to the Hacker’s PC.
- Run any program on the Victims PC.
- Display any Violating Image on victim’s Screen.
- Open the CD Drive of the Victim’s PC.
- Open any Web page on the Victims Screen.
- Disable any Specific Key or whole Keyboard.
- Shutdown Victim’s PC.
- Start a Song on the Victim’s PC.etc.etc…………..
Back Orifice / Back Orifice 2000
Back Orifice is one of the most common backdoor programs, and one of the most deadly. The name may seem like a joke, but sure, the threat is real. Back Orifice was established in Cult of the Dead Cow group. Back Orifice is an Open Source Program. The main Threat of this software is that by making some changes in the code anybody can make it undetectable to the Anti virus Program running on the Victim’s computer. Apart from the strange title, the program usually gets port 31337, the reference to “Lit” phenomenon is popular among hackers.
Back Orifice uses a client-server model, while the server and client is the victim attacker. What makes Back Orifice so dangerous that it can install and operate silently. There is not required interaction with the user in, meaning you could its on your computer right now, and do not know.
Companies such as Symantec have taken steps to protect computers against programs that they consider dangerous. But even more attacks using Back Orifice 2000. This is due partly to the fact that it is still evolving, as open source. As stated in the documentation the goal is ultimately the presence of the Back Orifice 2000 unknown even to those who installed it.
Back Orifice 2000, developed for Windows 95, Windows 98, Windows NT, Windows 2000 and Windows XP.
Where can I download Back orifice 2000?
Back Orifice 2000 can be downloaded at the following address: http://sourceforge.net/projects/bo2k/
I infected! How do I remove it?
Removing Back Orifice 2000 may require that you change the registry settings. To remove it at 7 simple steps, refer to the diagram below.
How do I delete Back orifice 2000
- Click Start> Run, and type “Regedit”(without the quotes)
- Follow the path below: HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServices “
- Now looking in the right box: “The umgr32 = ‘c: \ windows \ system \ umgr32.exe”
- Right-click on this entry and click Remove. Now restart your computer.
- After restarting only open Windows Explorer. Make sure you can see all registered extensions. To do so, select “View Options and configure the appropriate settings.
- Go to the WINDOWS \ SYSTEM directory, and find “umgr32.exe” file. Once you find it, delete it.
- Exit Windows Explorer and reboot again.
NetBus / Netbus 2.0 Pro
NetBus was established around the same time that the Back Orifice was in the late 1990’s. NetBus was originally designed as a program prank friends and family, of course anything too malicious. However, the program was released in 1998, and is widely used as a backdoor to manage computer.
Like the Back Orifice, NetBus allows attackers to do virtually everything in the computer victim. It also works well under Windows 9x systems, as well as Windows XP. Unlike Back Orifice, the latest version of NetBus regarded shareware is not free. NetBus is also implementing less stealthy operations, as a direct result of criticism and complaints of abusive use.
Where can I buy and download NetBus?
NetBus can be purchased and downloaded at the following address: http://www.netbus.org/
Ok, I am infected. Now what?
Fortunately, the latest version of NetBus is a valid program. It can be removed just like any other program. Previous issuance NetBus is a bit more tricky, however. If you are not lucky enough attacked with the latest version, the withdrawal process and in the Back Orifice.
How do I remove NetBus?
- Click Start> Run, and type “Regedit ‘(without the quotes)
- Follow the path below: HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServices “
- Now, in the right box, looking as follows: “[Name_of_Server].”Exe Of course, you have to find the actual name of this file EXE-. Usually This” Patch.exe ‘or’ SysEdit.exe “, but may vary.
- Reboot and remove all traces of the actual program, which can be left. Additionally, you can set yourself NetBus, and then use its own function disposal.
SubSeven / Sub7
SubSeven or Sub7, has been established for the same purpose was to NetBus pranks. Sub7 actually has more support for pranks, and has more advanced users. Sub7 also widely used by the script kiddies, although that many firewalls and anti-virus software before initialization.
Since Sub7 not supported for several years, the threat is usually very low. Most security programs will not have any problem in ending Sub7 before it has a chance to be started. This shows that the importance to the modernization and security programs is critical, because the money was still there.
Nevertheless, it is widely used by those who have physical access to your firewall, or security programs. If access rights, the tool will work without restrictions.
Where can I buy and download Sub7?
Sub7 not supported more, and hence is not available for download on any legitimate websites. If you were to make a Google search, you would find links to download Sub7. However, this is not the official site, and should be considered dubious and dangerous.
Sounds harmless, How do I remove it?
- End of the following processes through the curator: “editserver.exe, subseven.exe”
- Delete the following files: “editserver.exe, subseven.exe, tutorial.txt.”
Why these programs is absolutely legitimate?
All the basis behind these programs is that they are designed to help people, not harm. While some like NetBus really were originally created for pranks, they switched routes to avoid legal problems.
These programs claim to be the legitimate remote desktop program, although they certainly easily used for malicious use. These programs really should be used to aid or customer support departments. Why all adolescents is to copy these programs goes beyond us, but leave the content of their networks, while computer is a good idea.
The advent of new technology has made these programs in some respects less effective. However, programs such as Back Orifice 2000, yet still evolving, so do not be surprised to learn that he works in the background, waiting for instructions. Since the best defense is a good offense, be sure to save a sharp eye on what is installed on the network computers. After all, an ounce of prevention is worth a pound of cure.
Best Windows Hacking Tools
This is the Collection of Best Windows Hacking Tools:
1. Cain & Abel - Cain & Abel is a password recovery tool for the Microsoft Windows Operating System. It allows easy recovery of various kind of passwords by sniffing the network, cracking encrypted passwords using Dictionary, Brute-Force and Cryptanalysis attacks, recording VoIP conversations, decoding scrambled passwords, revealing password boxes, uncovering cached passwords and analyzing routing protocols.
2. SuperScan - SuperScan is a powerful TCP port scanner, pinger, resolver. SuperScan 4 (Current Version) is a completely-rewritten update of the highly popular Windows port scanning tool, SuperScan.
3. GFI LANguard Network Security Scanner - GFI LANguard N.S.S. is a network vulnerability management solution that scans your network and performs over 15,000 vulnerability assessments. It identifies all possible security threats and provides you with tools to patch and secure your network. GFI LANguard N.S.S. was voted Favorite Commercial Security Tool by NMAP users for 2 years running and has been sold over 200,000 times!
4. Retina - Retina Network Security Scanner, recognised as the industry standard for vulnerability assessment, identifies known security vulnerabilities and assists in prioritising threats for remediation. Featuring fast, accurate, and non-intrusive scanning, users are able to secure their networks against even the most recent of discovered vulnerabilities.
5. SamSpade - SamSpade provides a consistent GUI and implementation for many handy network query tasks. It was designed with tracking down spammers in mind, but can be useful for many other network exploration, administration, and security tasks. It includes tools such as ping, nslookup, whois, dig, traceroute, finger, raw HTTP web browser, DNS zone transfer, SMTP relay check, website search, and more.
6. N-Stealth - N-Stealth is a commercial web server security scanner. It is generally updated more frequently than free web scanners such as whisker and nikto, but you have to pay for the privilege.
7. Solarwinds - Solarwinds contains many network monitoring, discovery and attack tools. The advanced security tools not only test internet security with the SNMP Brute Force Attack and Dictionary Attack utilities but also validate the security on Cisco Routers with the Router Security Check. The Remote TCP Reset remotely display all active sessions on a device and the Password Decryption can decrypt Type 7 Cisco Passwords. The Port Scanner allows testing for open TCP ports across IP Address and port ranges or selection of specific machines and ports.
8. Achilles - The first publicly released general-purpose web application security assessment tool. Achilles acts as a HTTP/HTTPS proxy that allows a user to intercept, log, and modify web traffic on the fly. Due to a cyber squatter, Achilles is no longer online at its original home of www.Digizen-Security.com…OOPS!
9. CookieDigger - CookieDigger helps identify weak cookie generation and insecure implementations of session management by web applications. The tool works by collecting and analyzing cookies issued by a web application for multiple users. The tool reports on the predictability and entropy of the cookie and whether critical information, such as user name and password, are included in the cookie values.
10. Netcat (The Network SwissArmy Knife) - Netcat was originally a Unix utility which reads and writes data across network connections, using TCP or UDP protocol. It is designed to be a reliable “back-end” tool that can be used directly or easily driven by other programs and scripts. At the same time, it is a feature-rich network debugging and exploration tool, since it can create almost any kind of connection you would need and has several interesting built-in capabilities.
8 in 1 Keylogger with Cracks
- Sureshot Ghost Keylogger v.3.80
- Quick Keylogger 2.1.027
- Embrace
- Family Key Logger
- Easy Keyboard Logger v.1.0
- Blazingtools Perfect Keylogger v.1.6.2.0
- Ardamax Keylogger v.1.9
Free Download
 8 in 1 Keylogger with Cracks
8 in 1 Keylogger with CracksPassword:ghanshyam_thori
Call phones from Gmail- Calls from PC to Phone with Google Talk ~~~~ Now in India ~~~~
Free International Calls from PC to Phone with Google Talk and Talkster (GTalk-to-VoIP) Google has officially unveiled its new Google Mai...

-
This post deals with a few useful Firefox Add-ons, which makes your Firefox more comfortable than before. Tiny Menu : If you are not using ...
-
Google has launched a contacts manager that users of services like Google Docs, Picasa, and Calendar can use, without having to be a Gmail u...